Objective 5: AD Privilege Discovery
The Objective
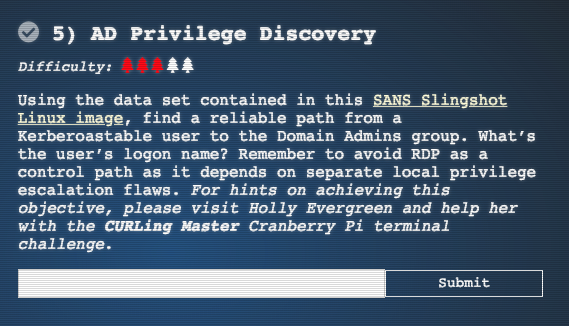
Hints by Holly Evergreen
The Solution
I downloaded an image put out by the incredible Jeff McJunkin
After changing the base memory to 8GB and setting the OS to Debian x64, I was able to log in
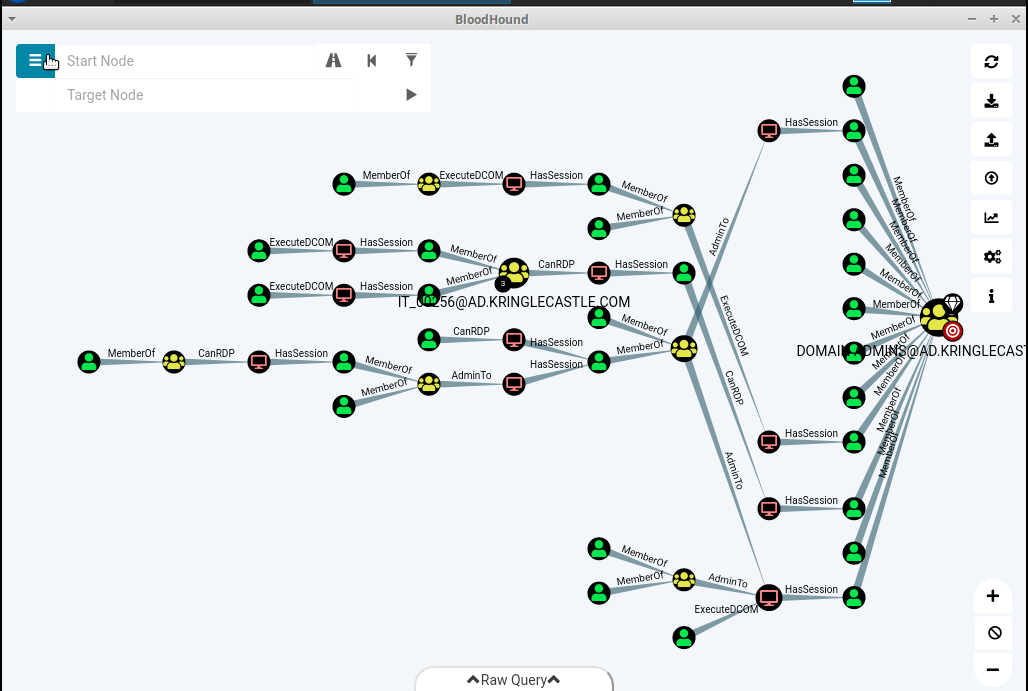
Bloodhound is already installed. I opened it up and get a diagram that shows users to the domain
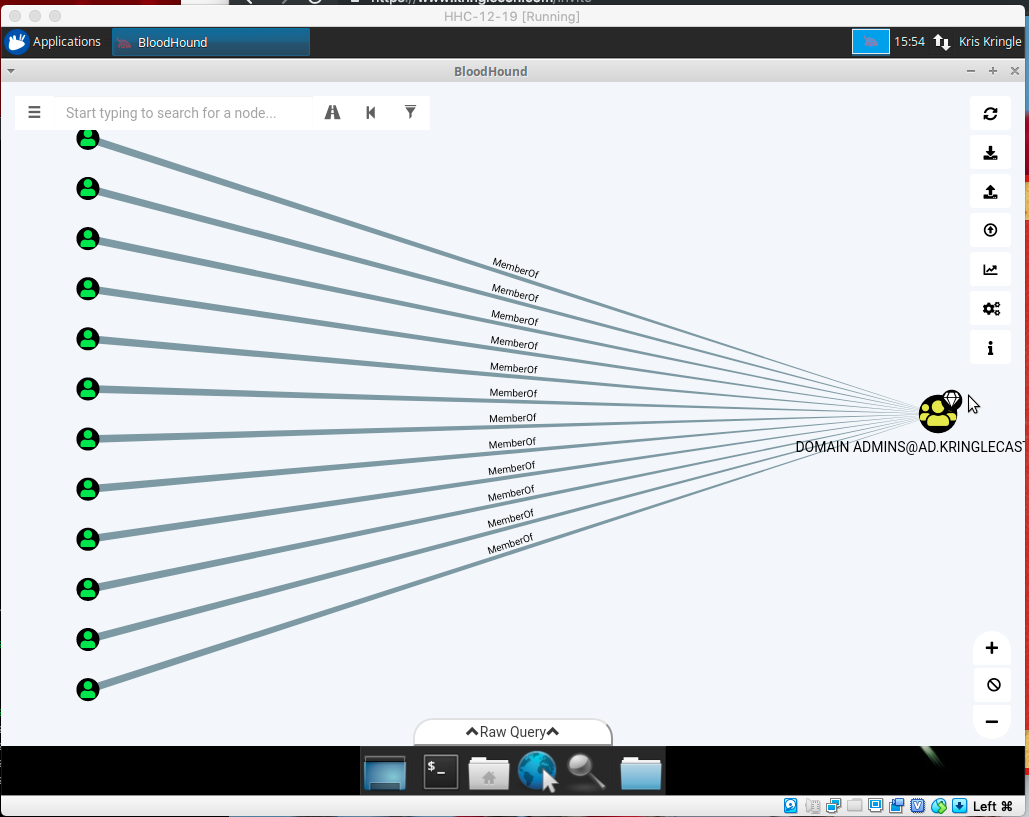
I select the “Shortest Path” and get this image
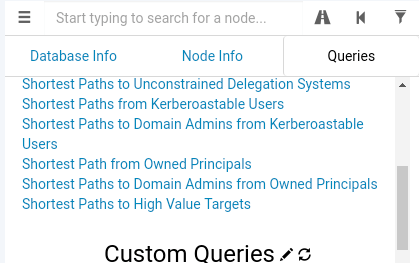
But, the right query is “Shortest Paths to Domain Admins from Kerberoastable Users”
These were all the possible users.
LDUBEJ00320@AD.KRINGLECASTLE.COM SMARCELLA00089@AD.KRINGLECASTLE.COM MTETTER00299@AD.KRINGLECASTLE.COM LDUBEJ00320@AD.KRINGLECASTLE.COM ZANDERA00437@AD.KRINGLECASTLE.COM JGUMBEL00486@AD.KRINGLECASTLE.COM ELANGONI00222@AD.KRINGLECASTLE.COM JFOX00132@AD.KRINGLECASTLE.COM AMARCELLA0089@AD.KRINGLECASTLE.COM RLOEFFELHOLZ0041@AD.KRINGLECASTLE.COM GLEONPACHER00047@AD.KRINGLECASTLE.COM RHEYDEL00118@AD.KRINGLECASTLE.COM JBETAK00084@AD.KRINGLECASTLE.COM
Based on the hint that RDP would not be a good path, I eliminated the ones that needed RDP. I reran the query and retrieved these
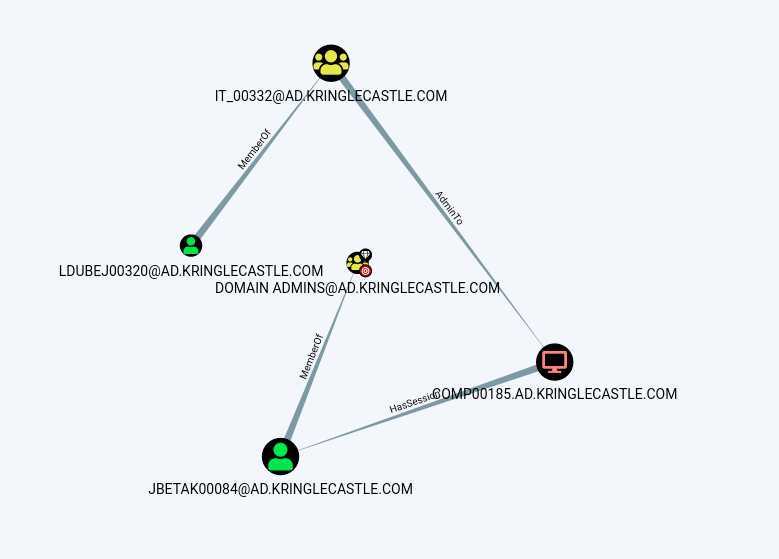
That left just two users
LDUBEJ00320@AD.KRINGLECASTLE.COM JBETAK00084@AD.KRINGLECASTLE.COM
Trying LDUBEJ0032 on the first try was the right one.
ANSWER: LDUBEJ00320@AD.KRINGLECASTLE.COM
The Narrative
Hans Is Making An Announcement