Objective 8: Network Traffic Forensics
The Objective
Hints by SugarPlum Mary
The Solution
The website is a network packet analyzer website. I created an account and logged in
After logging in, you can SNIFF TRAFFIC which will sniff 20 seconds of network traffic
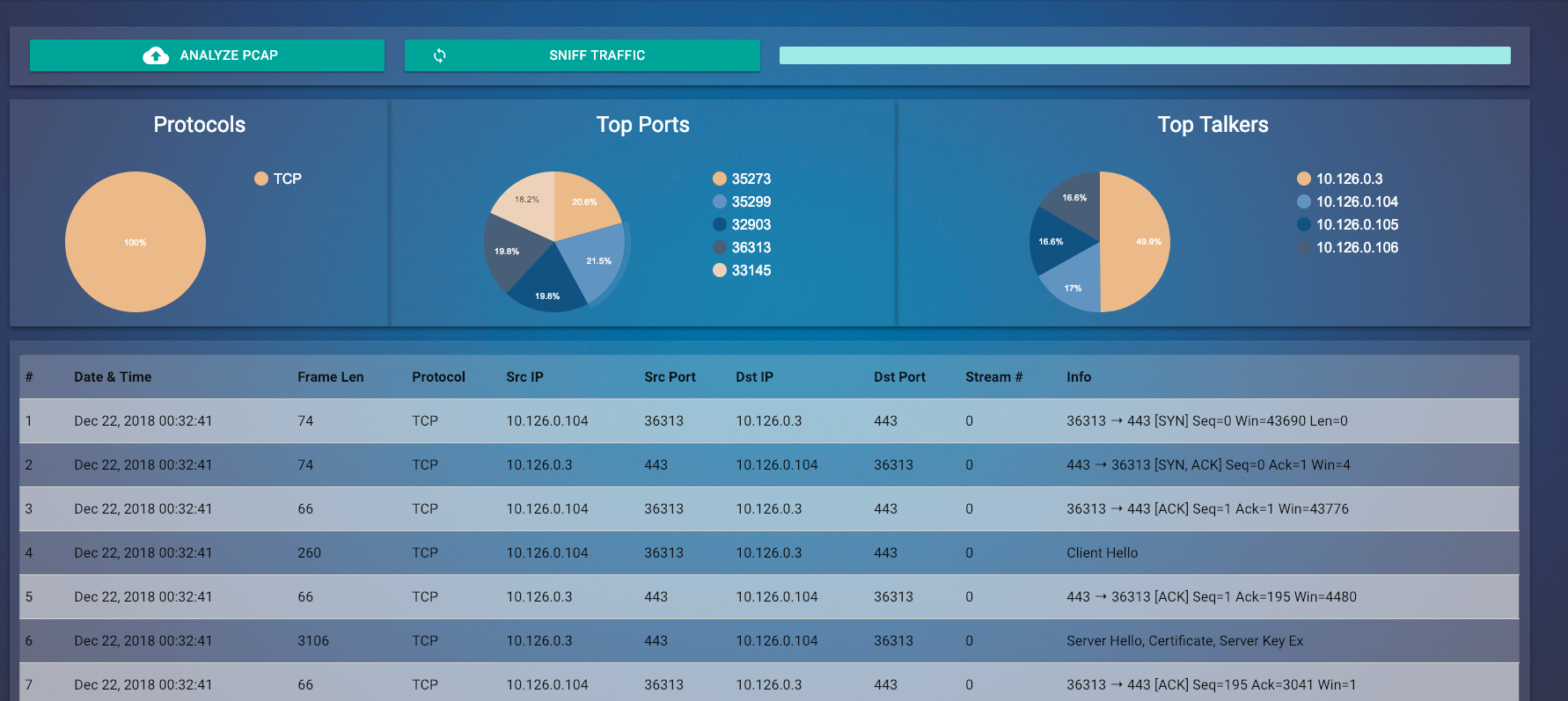
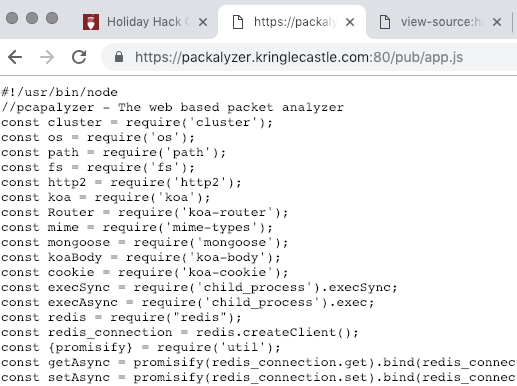
From the hint, we know that we need to look for HTML comments to find a dev file. The HTML comments describe an app.js file.
That file was accessible from the browser
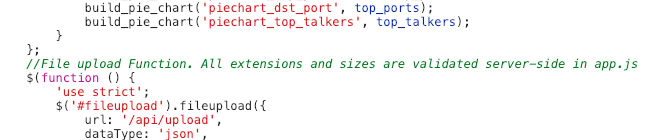
Opening that file, there were two areas of interest. First, there is an SSLKEYLOGFILE turned on. This is a file that the server will create that stores SSH Keys. We can use these keys to decrypt the SSL Traffic in Wireshark per Chris Davis’ talk (https://www.youtube.com/watch?v=YHOnxlQ6zec)
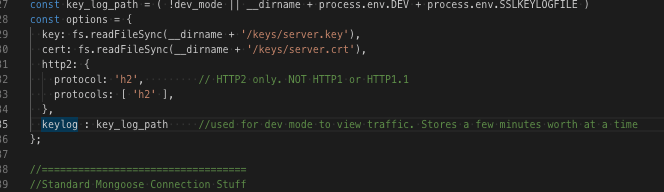
The location of the file is the directory
__dirname/process.env.DEV/process.env.SSLKEYLOGFILE
__dirname - the current directory from where execution happens
process.env.DEV - an environment variable DEV
process.env.SSLKEYLOGFILE - likely the file name
I needed to extract these two variables. I found this in the code:
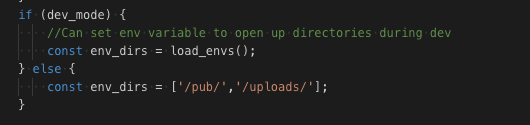
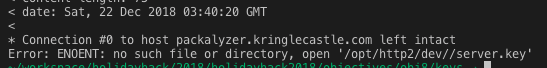
In DEV Mode (which is set), then allow all environment variables to be directories that are browsable. Combining this with the hint from SugarPlum, I started using curl to manipulate URL calls.
I found that if I requested a URL where the directory browsing was allowed, ie there was an environment variable name, then I received a different error than if the directory is not browsable.
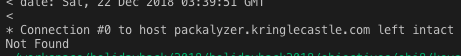
NOT BROWSABLE
BROWSABLE
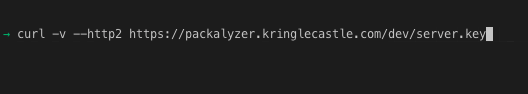
Picking “dev” was completely random, and it actually confused me. After some time being frustrated, I just threw in a weird URL and turned out to give me the answer I wanted. I did not think that the message that was being returned would evaluate the input directory as a variable.
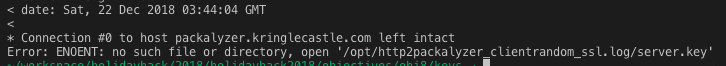
From the return value, we see that:
process.env.SSLKEYLOGFILE = packalyzer_clientrandom_ssl.log
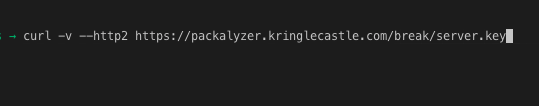
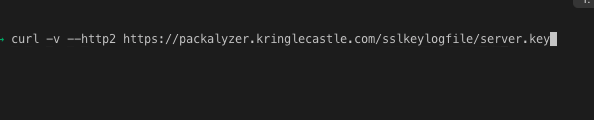
Retrieving the file just required evaluating process.env.DEV and retrieving the file
curl -v --http2 https://packalyzer.kringlecastle.com/dev/packalyzer_clientrandom_ssl.log >> packalyzer_clientrandom_ssl.txt
With the SSL Keys, I downloaded a packat capture and used Wireshark to evaluate the SSL. I found a JSON file with username and password information
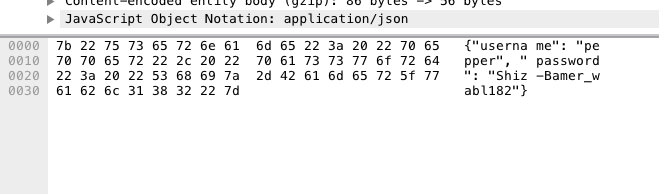
There were a number of other credentials pepper/Shiz-Bamer_wabl182 alabaster/Packer-p@re-turntable192 bushy/Floppity_Floopy-flab19283
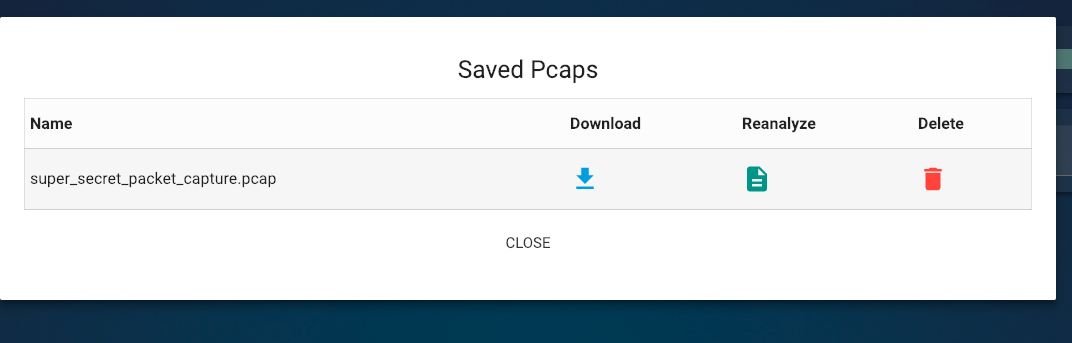
I logged into the Packalyzer with the credentials from Alabaster. There is a file with the “super secret packet capture”
Using Wireshark, I found an email from Holly to Alabaster with an attachment
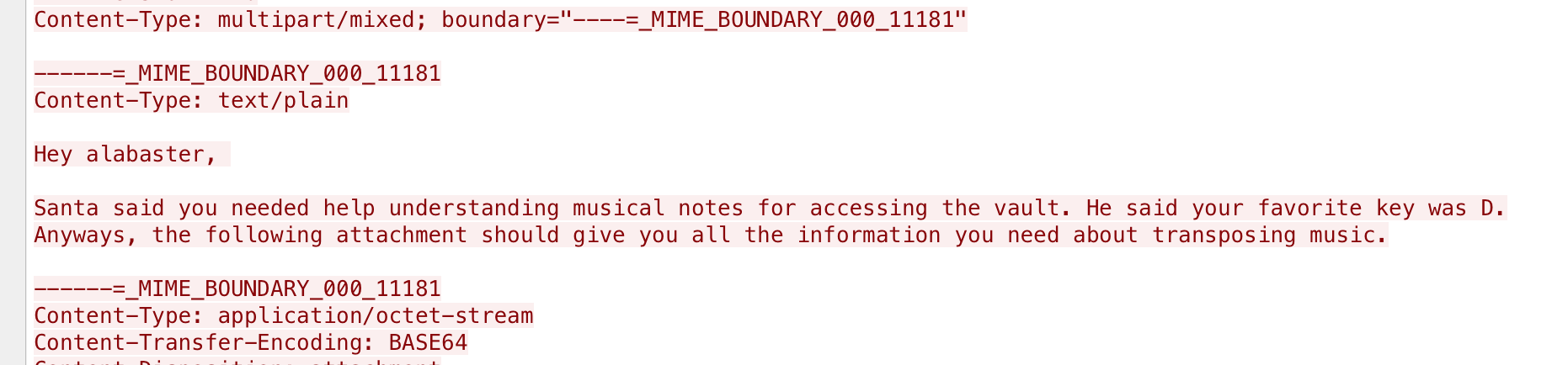
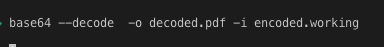
Copying the attachment to a file and running base64 decode out to a PDF
This provided the PDF that is talking about transposing on a piano, and the name of the song